Exploiting the latest max-severity ConnectWise bug is 'embarrassingly easy'
Tan KW
Publish date: Thu, 22 Feb 2024, 07:43 AM
Infosec researchers say urgent patching of the latest remote code execution (RCE) vulnerability in ConnectWise's ScreenConnect is required given its maximum severity score.
The vulnerability has been given a maximum 10/10 CVSS rating by ConnectWise, one that outside researchers agree with given the potential consequences of a successful exploit.
In disclosing the maximum-severity authentication bypass vulnerability (CWE-288), ConnectWise also revealed a second weakness - a path traversal flaw (CWE-22) with an 8.4 severity rating.
The company's initial February 19 disclosure mentioned there being no evidence to suggest that the vulnerabilities, neither of which yet have CVE identifiers, were being actively exploited but this has since changed.
ConnectWise updated its advisory yesterday to say it had received a few reports about compromised accounts.
Researchers at Horizon 3, who looked into the flaws, said they were also able to develop working exploits and that doing so was "extremely trivial."
At the start of this working week, researchers at Huntress were also able to develop a working exploit using both vulnerabilities, but decided to hold off publishing details at the time because there was no evidence of them being used in active attacks.
Since attacks were later confirmed to be taking place by ConnectWise, Huntress released its full analysis of the vulnerabilities, along with a proof-of-concept (PoC) exploit.
"The exploit is trivial and embarrassingly easy," Huntress said.
To achieve RCE, Huntress demonstrated its method to target the ScreenConnect setup wizard on machines that already had the software installed.
If an attacker is able to launch the setup wizard, they only need to partially complete the process - the part that registers the initial admin user to get things in motion. By registering the initial admin user and skipping the rest, the internal user database will be overwritten, deleting all local users except the one specified by the attacker.
"Once you have administrative access to a compromised instance, it is trivial to create and upload a malicious ScreenConnect extension to gain RCE," Huntress said. "This is not a vulnerability, but a feature of ScreenConnect, which allows an administrator to create extensions that execute .Net code as SYSTEM on the ScreenConnect server."
The path traversal vulnerability can also lead to Zip Slip attacks, the researchers said, but would require an attacker to have admin-level access in order to achieve RCE with it.
This vulnerability would be exploitable after taking advantage of the authentication bypass flaw, which itself would offer attackers RCE, so performing a Zip Slip attack wasn't exactly necessary.
The main difference here and the reason for highlighting its capabilities is that this vulnerability doesn't require an extension to be installed to run the malicious code, Huntress said, meaning it could be more difficult to detect.
As ever when PoCs are released, the likelihood of attacks proliferating is always high so urgent patching really is of the essence.
Plus, with attacks targeting remote monitoring and management (RMM) tools, the potential for attackers to operate as local users presents a severe threat to any IT environment.
All versions of ScreenConnect before and including 23.9.7 are affected by the vulnerabilities, but only self-hosted and on-prem installations since cloud customers should already have had their updates applied.
"For on-premise users, we offer our strongest recommendation to patch and update to ScreenConnect version 23.9.8 immediately," Huntress said.
ConnectWise said it will be releasing fixed versions of releases 22.4 through 23.9.7 soon, but the recommendation is, like in most cases where possible, to upgrade to the latest available version.
For those looking to perform threat hunting in their environments, limited indicators of compromise are available so far. There are just three IP addresses used by attackers in the incidents the vendor has seen:
-
155.133.5.15
-
155.133.5.14
-
118.69.65.60
"These indicators can be incorporated into your cybersecurity monitoring platform," said ConnectWise in its advisory. "They can help you stop a cyberattack that's in progress. Plus, you can use IOCs to find ways to detect and stop ransomware, malware, and other cyberthreats before they cause data breaches."
It should be said that there are no temporary mitigation steps provided in lieu of patching so upgrading really is the only way out of this.
Data from internet monitoring biz Shadowserver indicates that there are around 3,800 vulnerable ConnectWise instances currently running, with the vast majority located in the US. ®
https://www.theregister.com//2024/02/21/connectwise_max_severity_bug/
More articles on Future Tech
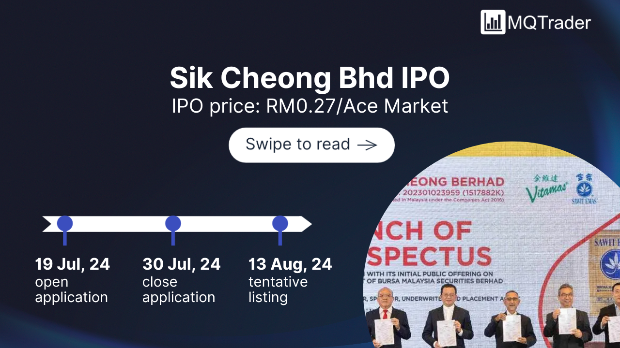
Created by Tan KW | Jul 27, 2024
Created by Tan KW | Jul 27, 2024
Created by Tan KW | Jul 27, 2024