Why entrepreneurs need to consider increasing their digital security
Tan KW
Publish date: Sat, 20 Apr 2024, 02:35 PM
The way we live, work, play, and communicate today is so tech dependent that it demands we always be on our devices as we go through our daily routines.
Understanding why this is the case doesn't take too much analysis. In the US alone, over 250 million adults own smartphones, with an average daily usage time of around 4.5 hours.
The picture becomes even clearer when you zoom out to a global scale to factor in the 6.9 billion smartphone users, 47.1% of private households that own a PC, and 5.3 billion active Internet users.
The growing global interconnectivity via the Internet has created opportunities for hackers and cybercriminals to prey on our devices and networks to steal sensitive personal and company information. Never in history has it been more pertinent for people to be informed about their device security - but the stats show that many are still lagging behind in this sense.
A study by cybersecurity solutions company Kaspersky put the percentage of global smartphone users without antivirus protection at 40%. That's an alarming amount of smartphones, especially if these devices are hooked up to the same network as other phones or computers that may or may not have some cybersecurity features enabled.
While hacking and data theft attempts are on the rise, there are ways to protect yourself from becoming a victim of cyberattacks. This is, of course, assuming you already use strong passwords, deploy two-factor authentication, filter people who get on to your network, and take other rudimentary security measures.
How regularly do you update your apps and devices?
This should go without saying, but there are many device owners who don't take this as seriously as they should. Another study done by Kaspersky laid out participants across a spectrum of responses they gave to how they responded to updates.
The findings showed that about 45%, on average, would install device updates daily on their work and personal devices, about 24% would update weekly, 18% update once a month, 11% do so several times a year, and just under 3% never install updates.
Device owners who rarely update their devices, if at all, are not intrigued by new themes or features. They love the familiarity of a device and are worried that an update could ruin everything.
However, updates are crucial, because they often come with more effective security patches to remedy vulnerabilities in a device's system. Ignoring these updates or letting them linger puts a device at much greater risk, especially since you most likely have all your sensitive accounts, like your banking or company information, logged in on it.
The potential damage if your device is hacked or stolen is not worth the risk. The commitment to regularly updating your operating system should also include your apps and your browsers, as these are possible doors for cybercriminals to leverage.
Encryption significantly reduces the possibility of data hacks or theft
Episodes of people losing their sensitive data to identity thieves are rife across cyberspace. Companies are not left out, losing on average US$9.48 mil per breach - and this is just for US companies.
Deploying encryption tools within your devices is crucial to protect this sensitive data by overwriting the data on your personal computer or network. You can decide how much of your info you want to encrypt. You could encrypt a select number of files or folders, or your entire disk, and external storage units like your flash drives.
Some operating systems come with inbuilt encryption capabilities, like BitLocker for Windows or Apple’s FileVault. But sometimes, depending on the sensitivity of your line of work or your personal security needs, you may need a more niche encryption solution that goes further.
Tools like Cradle Messenger, for instance, solve an encryption issue for people who want to remain anonymous and maintain the security of their chats and interactions with other people. This is a secure chat app that focuses on strengthening the promise of shielding users from past communications so that records of their correspondence will be untraceable.
Many popular chat apps today offer message security with features like disappearing messages, but flaws and vulnerabilities in the technology still exist. When subjected to intense forensic analysis, many of these apps have been known to divulge their secrets.
Most secure chat apps prioritise the encryption of message transmission. But what happens if someone else gets ahold of your device or that of the receiver?
“Our app overwrites data multiple times on the hard drive using the data sanitization standard required by the Department of Defense,” says Elizaveta Shevchenko, security research lead at Cradle. “Cradle Messenger also overwrites the RAM after every session with random data or zeroes. This tool is perfect for activists, whistleblowers, journalists, and other roles that handle sensitive information with possible life-altering consequences. This way, even if their devices fall into the wrong hands, it would be impossible to extract any information from them.”
What about when you're browsing online? Using a VPN is a wise choice, because of its ability to encrypt web traffic and shield your IP information, among other things.
At the very least, you could opt for browsing only in incognito mode when you want to visit questionable websites. Alternatively, you could go for incognito-focused browsers, like Tails, to stay anonymous and undetectable.
As technology evolves, cyberthreats are becoming more sophisticated. Cyber insecurity sits among the top five global risks over the next two years. Operating system providers and several app companies keep pushing the boundaries of security innovation to keep up with emerging threats, and they provide these to users, typically for free.
The onus is on the user to be proactive about developing a habit of always updating their devices and apps that could expose them to cyber risks while educating themselves on security best practices to mitigate the frequency or consequences of an attack.
- TNS
More articles on Good Articles to Share
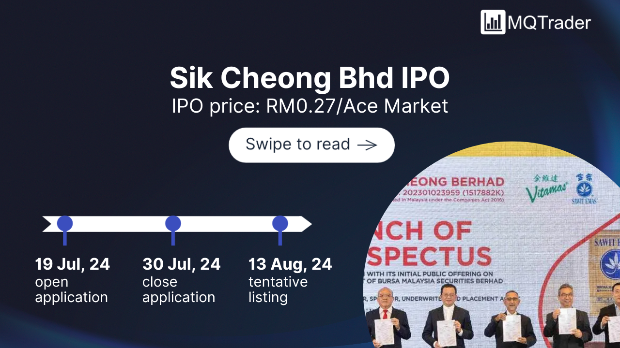
Created by Tan KW | Jul 27, 2024
Created by Tan KW | Jul 27, 2024