Tesla hacks make big bank at Pwn2Own's first automotive-focused event
Tan KW
Publish date: Mon, 29 Jan 2024, 10:15 AM
Infosec in brief Trend Micro's Zero Day Initiative (ZDI) held its first-ever automotive-focused Pwn2Own event in Tokyo last week, and awarded over $1.3 million to the discoverers of 49 vehicle-related zero day vulnerabilities.
Researchers from French security outfit Synacktiv took home $450,000 after demonstrating six successful exploits, one of which saw the company’s crew gain root access to a Tesla Modem. Another effort found a sandbox escape in the Musk-mobiles’ infotainment system.
Other popular targets at the three day event included after-market infotainment systems and, more troublingly, a whole host of successful hacks on EV chargers.
Five $60,000 bounties - the second-highest monetary awards behind Synacktiv's $100k Tesla hacks - were awarded for attacks on EV chargers manufactured by Emporia, ChargePoint, Ubiquiti, Phoenix and JuiceBox.
Three attacks against Automotive Grade Linux were also attempted, with only one succeeding (Synacktiv again). This vehicular cut of Linux is used as the backbone of infotainment systems by several automotive OEMs, including Subaru, Toyota and Lexus.
Given most of the bugs exploited at the event were newly reported zero days, little information about the nature of the flaws was revealed.
ZDI's next event will be its annual Pwn2Own fete in Vancouver from March 20-24, at which hackers will be able to demonstrate their prowess at exploiting vulnerabilities in a new category: Cloud native and container software.
For shame: SEC admits a SIM swapper hijacked its Twitter account
We had our suspicions when Twitter/X blamed the US Securities and Exchange Commission for the account takeover that led to the premature release of news the regulator would allow Bitcoin exchange-traded funds- and those suspicions have been confirmed.
"The SEC determined that the unauthorized party obtained control of the SEC cell phone number associated with the account in an apparent 'SIM swap' attack," the Commission admitted last week.
For those unfamiliar with this form of attack, SIM swaps involve convincing a telecom carrier to transfer a phone number to a new SIM card (a shift for which there are a variety of legitimate reasons), giving an attacker control over communications going to and from that number - like a second authentication factor.
That didn't matter, of course, because the SEC also admitted it disabled multi-factor authentication with Twitter support in July last year "due to issues accessing the account," but no one bothered to turn it back on.
Time for some remedial security training.
Careful with those (macOS) cracks, Eugene
Downloaders of cracked macOS apps, beware: A newly discovered macOS malware family is making the rounds in cracked apps, and it's a doozy.
Spotted by threat researchers at Kaspersky's Securelist, the malware is hidden in previously cracked apps as an "activator" that forces itself to run when apps are installed. Once run, it retrieves a payload that includes a backdoor allowing controllers to execute arbitrary commands on infected machines, and then delivers a list of system information to the C2 server.
The goal of the malware appears to be stealing crypto wallet seed phrases, as the payload script also checks for installations of the Exodus cryptocurrency wallet. If detected, the malware swaps the installed version for a malicious replacement that transmits seed phrases to the C2 server as soon as the infected Exodus install is opened.
"There were no other new features" added to the infected install, Securelist noted.
Non-cryptobros should still be aware of this threat - the backdoor gives an attacker plenty of opportunity to wreak other havoc, and Securelist believes the malware is still a work in progress, so other nastiness could be added later. ®
https://www.theregister.com//2024/01/29/infosec_news_roundup_in_brief/
More articles on Future Tech
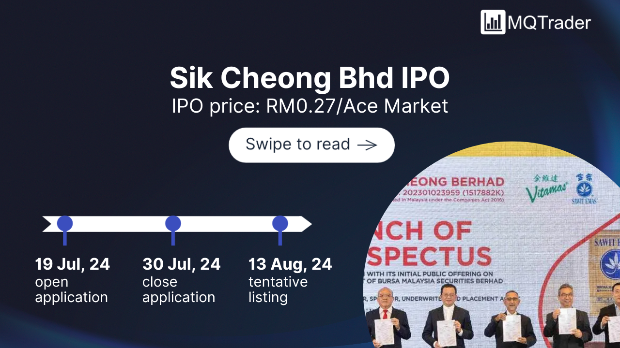
Created by Tan KW | Jul 30, 2024
Created by Tan KW | Jul 30, 2024
Created by Tan KW | Jul 30, 2024
Created by Tan KW | Jul 30, 2024
Created by Tan KW | Jul 30, 2024
Created by Tan KW | Jul 30, 2024